Learn Bug Bounty Hunting — From Zero to Real-World Impact
Temphack is an open, practical Bug Bounty Hunter community focused on real skills, real methodologies, and real learning.
From absolute beginner to advanced researcher — step by step, together.
Start Learning
What is Temphack?
Learn by Doing
No theory overload. We focus on hands-on learning, labs, walkthroughs, and real-world bug bounty workflows.
Grow Step by Step
Start as a beginner. Learn reconnaissance, web vulnerabilities, APIs, automation, and reporting — at your own pace.
Build Together
Temphack is not just a blog. It’s a growing community where knowledge is shared openly and responsibly.
Your Bug Bounty Learning Path
Learning Path
Beginner
- HTTP & how the web works
- Basic recon
- Understanding vulnerabilities
Intermediate
- Advanced recon & automation
- SQLi, XSS, IDOR, logic flaws
- API testing
Advanced
- Custom tooling
- Chaining vulnerabilities
- Advanced bug classes
Professional Mindset
- Responsible disclosure
- Writing high-quality reports
- Long-term consistency
Latest Bug Bounty Articles
Practical guides, walkthroughs, and mindset articles — written by someone actively learning and practicing bug bounty hunting.
-
Understanding HTTP for Bug Bounty Hunters

The Foundation of Web Security Testing very web vulnerability exists because of HTTP. Before learning SQL injection, XSS, IDOR, or API flaws, you must understand how browsers and servers communicate. Bug bounty hunting is not about payloads first — it is about observing behavior. This article explains HTTP in a bug bounty context, using clear examples and a mindset that prepares you for real-world testing. What Is HTTP (In Simple Terms)? HTTP (Hypertext Transfer Protocol) is the language used by: Every interaction follows the same basic pattern: If you understand this exchange, you understand where bugs live. The HTTP Request…
-
PowerShell Basics for Bug Bounty Hunters
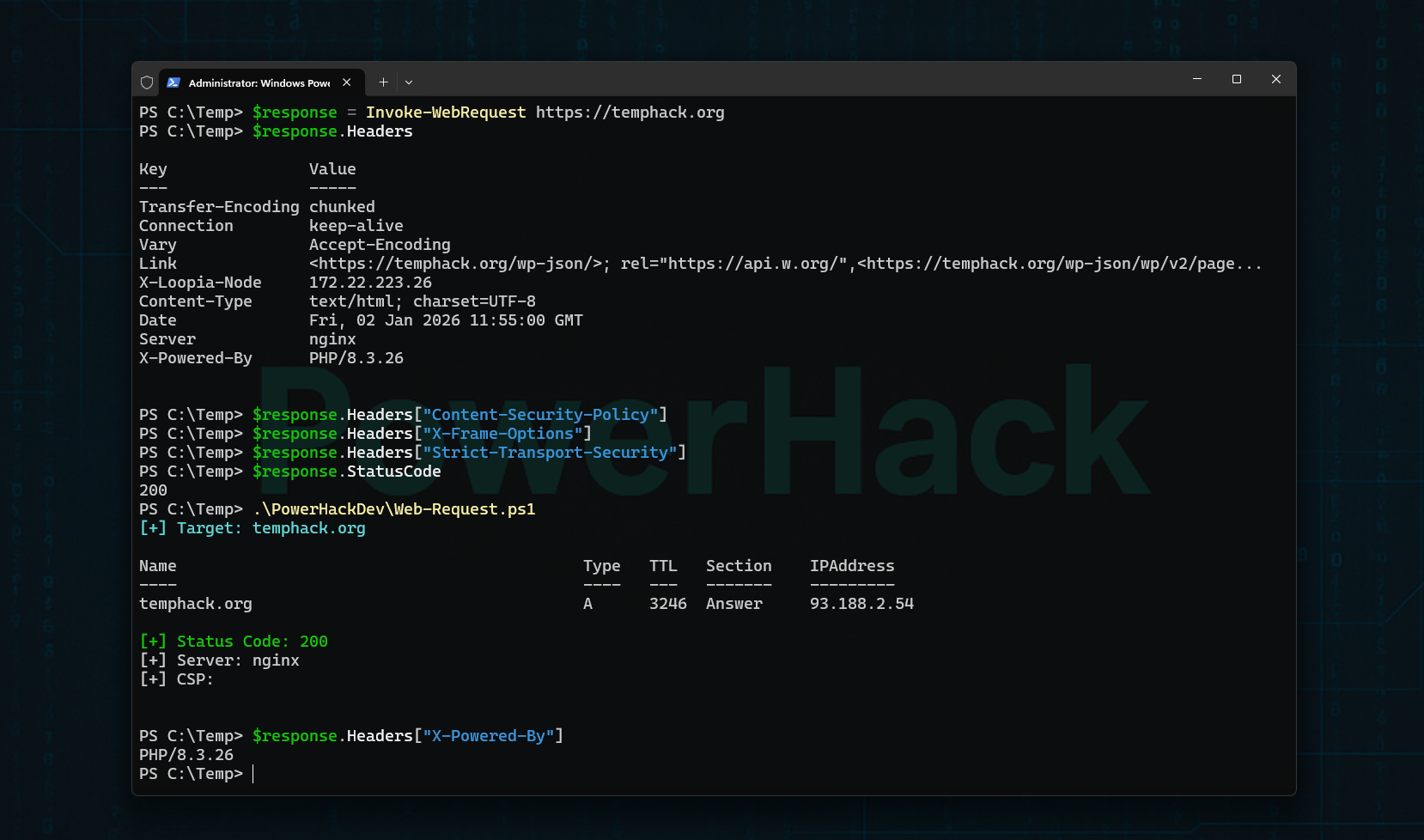
Using Your Own Domain for Safe, Legal Practice When people think about bug bounty hunting, they often assume Linux is required.In reality, what matters is understanding how systems work — not the operating system. PowerShell is a powerful, built-in automation and networking tool available on Windows. When used correctly, it allows you to explore how…
-
PowerHack: Bug Bounty Hunting From Windows

A common myth in hacking is that you must use Linux to be effective. PowerHack exists to challenge that idea. This article explains why Windows can be a powerful and legitimate bug bounty platform — and how PowerHack approaches hacking from Windows. Why Hack From Windows? Windows offers: What matters is understanding — not the…
-
Bug Bounty Basics: How Ethical Hackers Find Vulnerabilities
Many beginners ask the same question:“Where do I even start when hunting bugs?” The answer is not tools.The answer is methodology. This article explains the core workflow most ethical hackers follow when searching for vulnerabilities. Step 1: Understanding the Target Before touching any tools, experienced hunters: Understanding functionality often reveals more bugs than scanning. Step…
-
What Is Bug Bounty Hunting? A Beginner’s Introduction

Bug bounty hunting is one of the most practical and accessible ways to learn ethical hacking. Instead of attacking systems illegally, bug bounty hunters work with companies to find security vulnerabilities — and get rewarded for it. This article explains what bug bounty hunting really is, how it works, and what beginners should realistically expect…